Workflows is now in open beta, and available to any developer a free or paid Workers plan.
Workflows allow you to build multi-step applications that can automatically retry, persist state and run for minutes, hours, days, or weeks. Workflows introduces a programming model that makes it easier to build reliable, long-running tasks, observe as they progress, and programmatically trigger instances based on events across your services.
You can get started with Workflows by following our get started guide and/or using
npm create cloudflareto pull down the starter project:Terminal window npm create cloudflare@latest workflows-starter -- --template "cloudflare/workflows-starter"You can open the
src/index.tsfile, extend it, and usewrangler deployto deploy your first Workflow. From there, you can:- Learn the Workflows API
- Trigger Workflows via your Workers apps.
- Understand the Rules of Workflows and how to adopt best practices
It’s now easy to create wildcard-based URL Rewrites. No need for complex functions—just define your patterns and go.
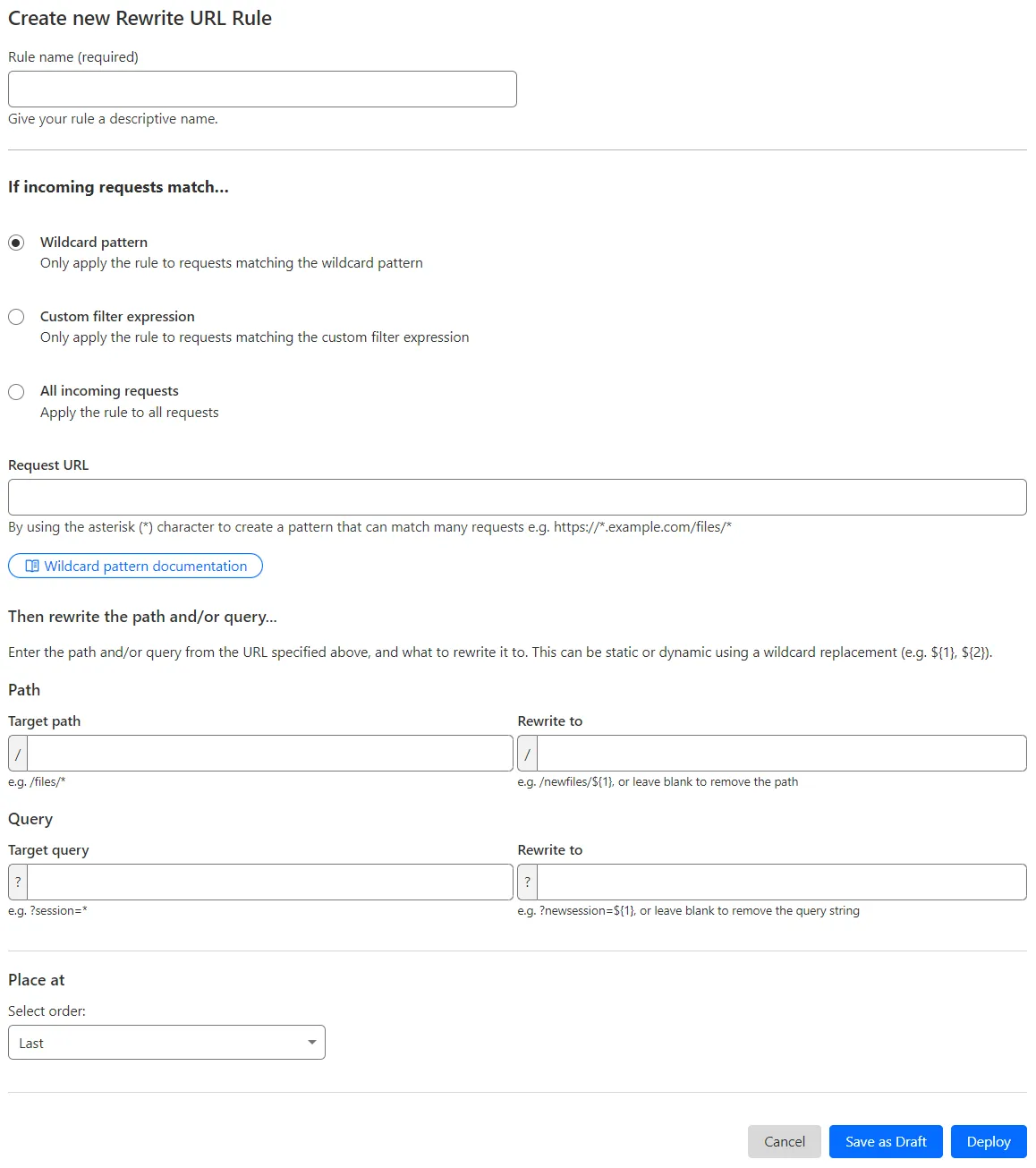
What’s improved:
- Full wildcard support – Create rewrite patterns using intuitive interface.
- Simplified rule creation – No need for complex functions.
Try it via creating a Rewrite URL rule in the dashboard.
Cloudflare has introduced new fields to two Gateway-related datasets in Cloudflare Logs:
-
Gateway HTTP:
ApplicationIDs,ApplicationNames,CategoryIDs,CategoryNames,DestinationIPContinentCode,DestinationIPCountryCode,ProxyEndpoint,SourceIPContinentCode,SourceIPCountryCode,VirtualNetworkID, andVirtualNetworkName. -
Gateway Network:
ApplicationIDs,ApplicationNames,DestinationIPContinentCode,DestinationIPCountryCode,ProxyEndpoint,SourceIPContinentCode,SourceIPCountryCode,TransportProtocol,VirtualNetworkID, andVirtualNetworkName.
-
The Magic Firewall dashboard now allows you to search custom rules using the rule name and/or ID.
- Log into the Cloudflare dashboard ↗ and select your account.
- Go to Analytics & Logs > Network Analytics.
- Select Magic Firewall.
- Add a filter for Rule ID.
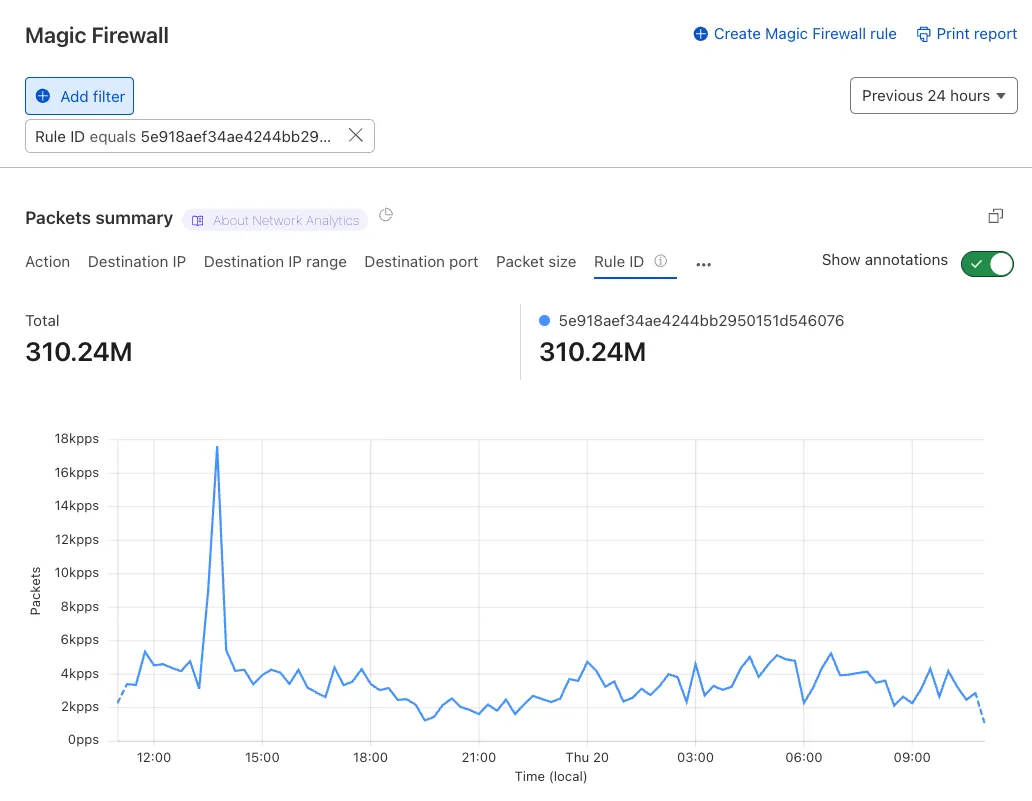
Additionally, the rule ID URL link has been added to Network Analytics.
Organizations can now eliminate long-lived credentials from their SSH setup and enable strong multi-factor authentication for SSH access, similar to other Access applications, all while generating access and command logs.
SSH with Access for Infrastructure uses short-lived SSH certificates from Cloudflare, eliminating SSH key management and reducing the security risks associated with lost or stolen keys. It also leverages a common deployment model for Cloudflare One customers: WARP-to-Tunnel.
SSH with Access for Infrastructure enables you to:
- Author fine-grained policy to control who may access your SSH servers, including specific ports, protocols, and SSH users.
- Monitor infrastructure access with Access and SSH command logs, supporting regulatory compliance and providing visibility in case of security breach.
- Preserve your end users' workflows. SSH with Access for Infrastructure supports native SSH clients and does not require any modifications to users’ SSH configs.
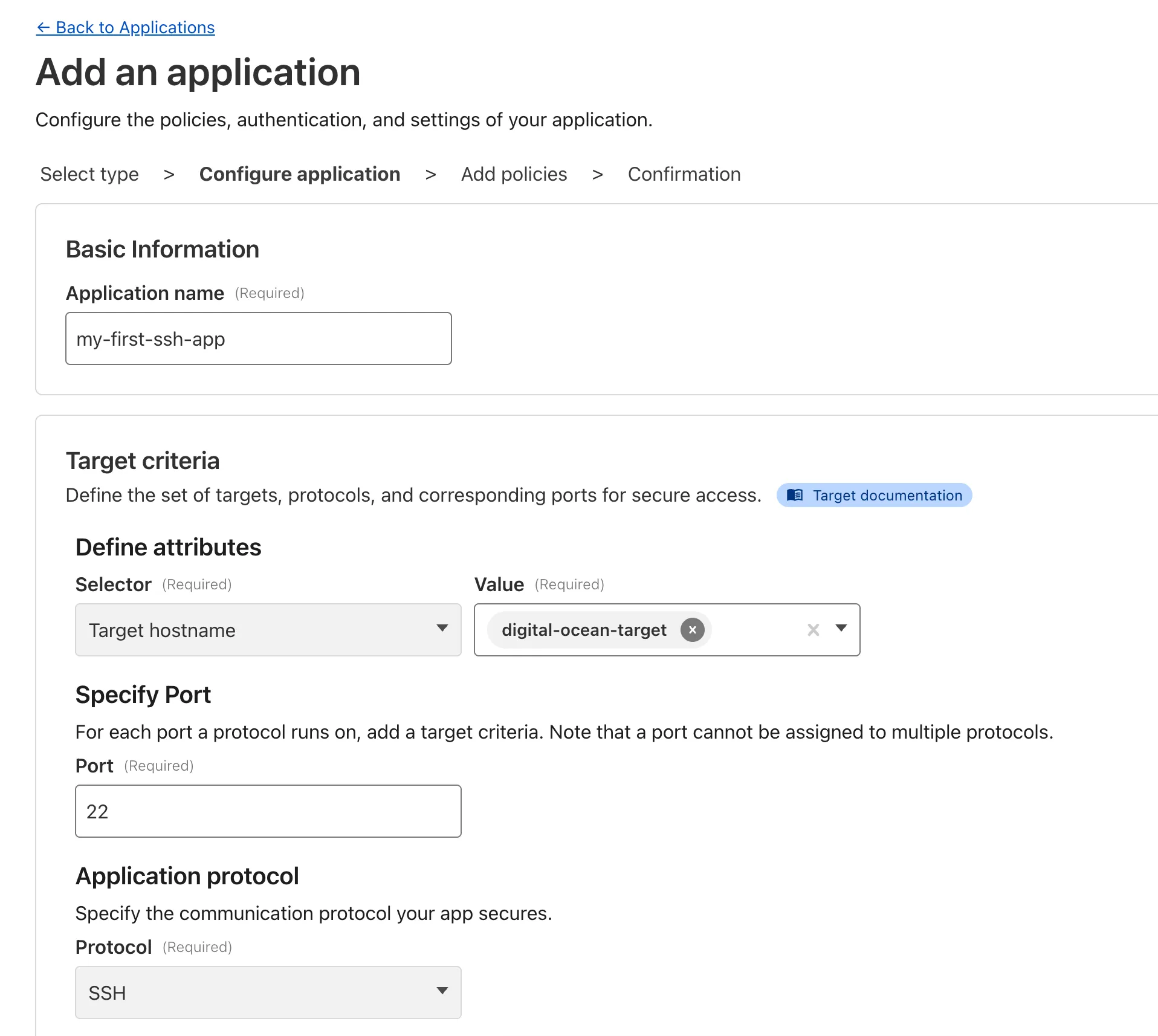
To get started, refer to SSH with Access for Infrastructure.
The free version of Magic Network Monitoring (MNM) is now available to everyone with a Cloudflare account by default.
- Log in to your Cloudflare dashboard ↗, and select your account.
- Go to Analytics & Logs > Magic Monitoring.
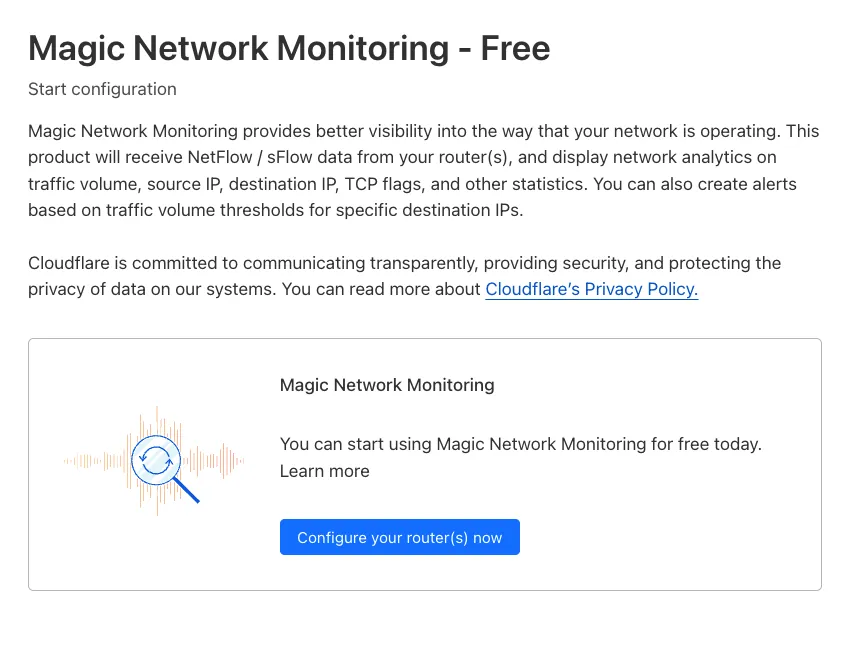
For more details, refer to the Get started guide.
Every site on Cloudflare now has access to AI Audit, which summarizes the crawling behavior of popular and known AI services.
You can use this data to:
- Understand how and how often crawlers access your site (and which content is the most popular).
- Block specific AI bots accessing your site.
- Use Cloudflare to enforce your
robots.txtpolicy via an automatic WAF rule.
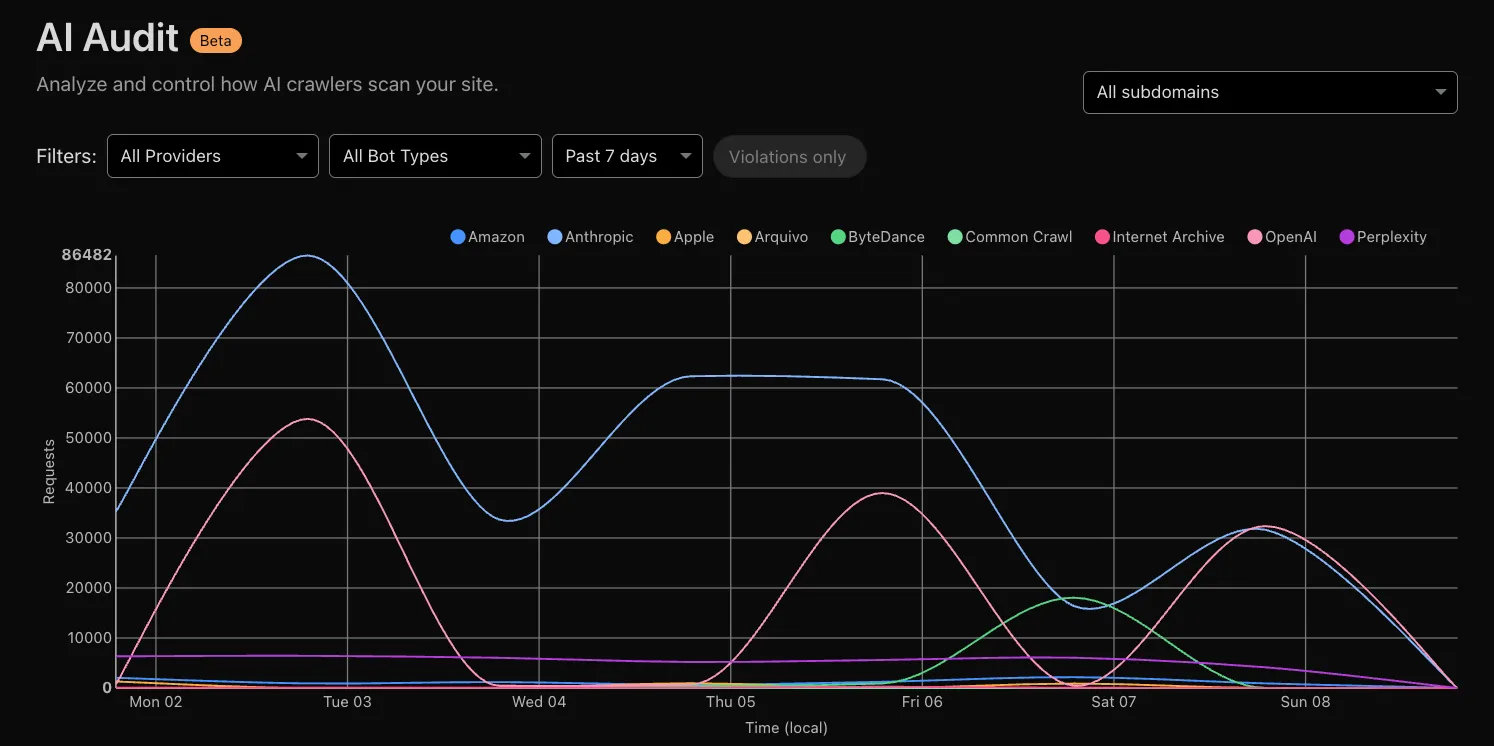
To get started, explore AI audit.
You can now create optimized cache rules instantly with one-click templates, eliminating the complexity of manual rule configuration.
- Navigate to Rules > Templates in your Cloudflare dashboard.
- Select a template for your use case.
- Click to apply the template with sensible defaults.
- Customize as needed for your specific requirements.
- Cache everything: Adjust the cache level for all requests.
- Bypass cache for everything: Bypass cache for all requests.
- Cache default file extensions: Replicate Page Rules caching behavior by making only default extensions eligible for cache.
- Bypass cache on cookie: Bypass cache for requests containing specific cookies.
- Set edge cache time: Cache responses with status code between 200 and 599 on the Cloudflare edge.
- Set browser cache time: Adjust how long a browser should cache a resource.
To get started, go to Rules > Templates ↗ in the dashboard. For more information, refer to the Cache Rules documentation.
Now, you can create common rule configurations in just one click using Rules Templates.
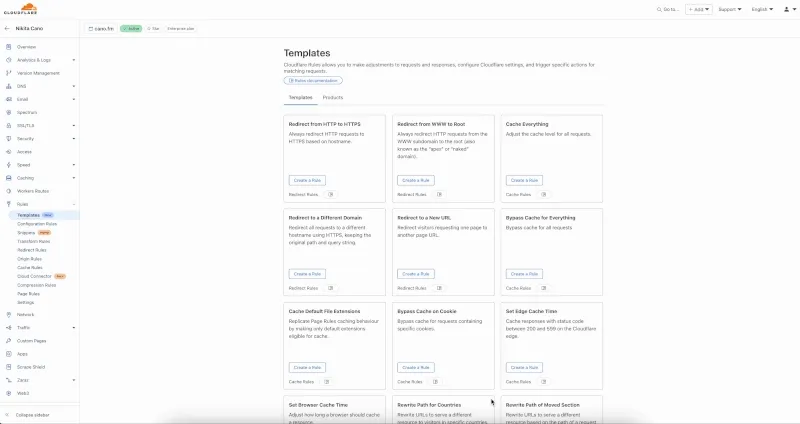
What you can do:
- Pick a pre-built rule – Choose from a library of templates.
- One-click setup – Deploy best practices instantly.
- Customize as needed – Adjust templates to fit your setup.
Template cards are now also available directly in the rule builder for each product.
Need more ideas? Check out the Examples gallery in our documentation.
You can now achieve higher cache hit ratios with Generic Global Tiered Cache. Regional content hashing routes content consistently to the same upper-tier data centers, eliminating redundant caching and reducing origin load.
Regional content hashing groups data centers by region and uses consistent hashing to route content to designated upper-tier caches:
- Same content always routes to the same upper-tier data center within a region.
- Eliminates redundant copies across multiple upper-tier caches.
- Increases the likelihood of cache HITs for the same content.
A popular image requested from multiple edge locations in a region:
- Before: Cached at 3-4 different upper-tier data centers
- After: Cached at 1 designated upper-tier data center
- Result: 3-4x fewer cache MISSes, reducing origin load and improving performance
To get started, enable Generic Global Tiered Cache on your zone.
Beyond the controls in Zero Trust, you can now exchange user risk scores with Okta to inform SSO-level policies.
First, configure Cloudflare One to send user risk scores to Okta.
- Set up the Okta SSO integration.
- In the Cloudflare dashboard ↗, go to Zero Trust > Integrations > Identity providers.
- In Your identity providers, locate your Okta integration and select Edit.
- Turn on Send risk score to Okta.
- Select Save.
- Upon saving, Cloudflare One will display the well-known URL for your organization. Copy the value.
Next, configure Okta to receive your risk scores.
- On your Okta admin dashboard, go to Security > Device Integrations.
- Go to Receive shared signals, then select Create stream.
- Name your integration. In Set up integration with, choose Well-known URL.
- In Well-known URL, enter the well-known URL value provided by Cloudflare One.
- Select Create.
Welcome to your new home for product updates on Cloudflare One.
Our new changelog lets you read about changes in much more depth, offering in-depth examples, images, code samples, and even gifs.
If you are looking for older product updates, refer to the following locations.
You can now easily enable Real User Monitoring (RUM) monitoring for your hostnames, while safely dropping requests from visitors in the European Union to comply with GDPR and CCPA.
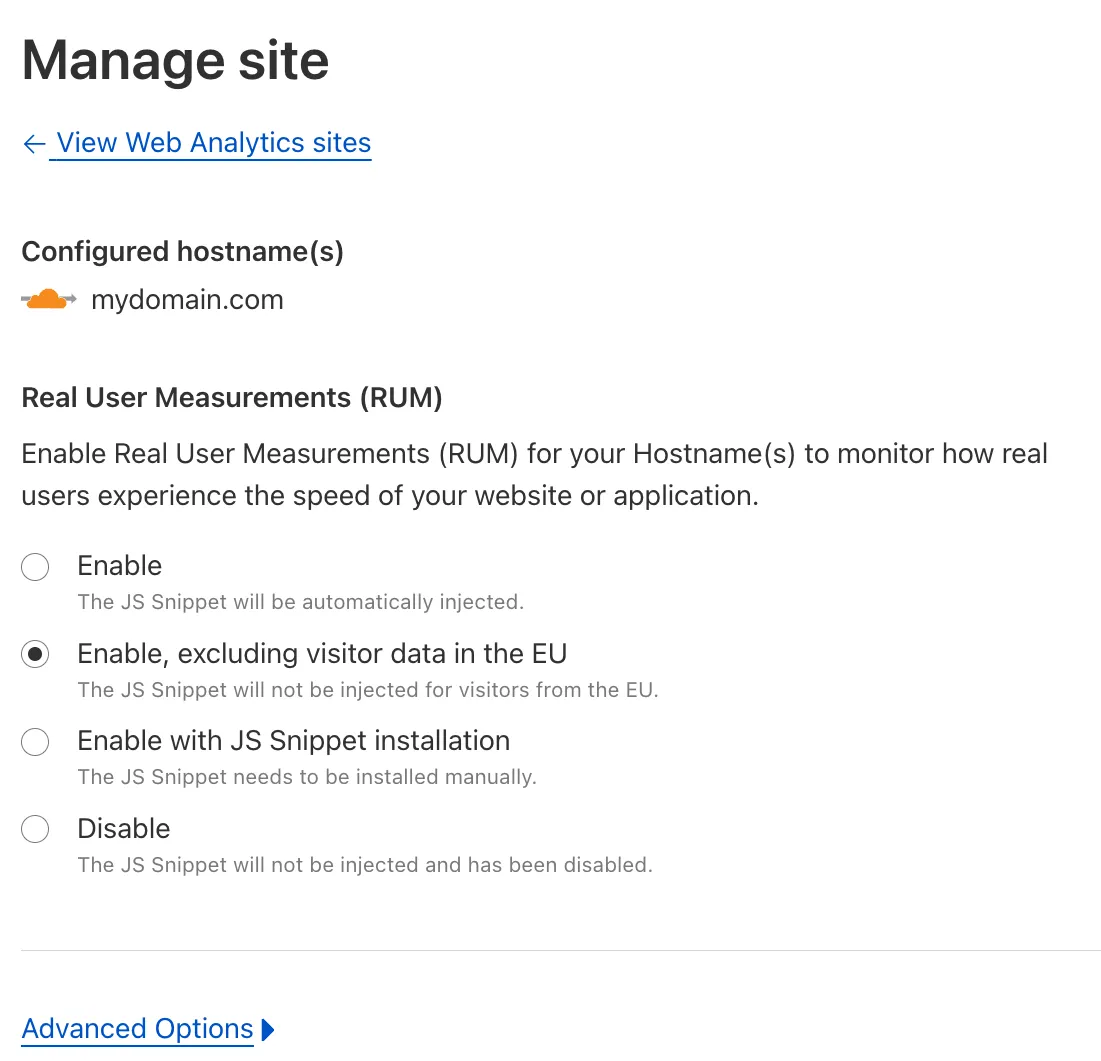
Our Web Analytics product has always been centered on giving you insights into your users' experience that you need to provide the best quality experience, without sacrificing user privacy in the process.
To help with that aim, you can now selectively enable RUM monitoring for your hostname and exclude EU visitor data in a single click. If you opt for this option, we will drop all metrics collected by our EU data centers automatically.
You can learn more about what metrics are reported by Web Analytics and how it is collected in the Web Analytics documentation. You can enable Web Analytics on any hostname by going to the Web Analytics ↗ section of the dashboard, selecting "Manage Site" for the hostname you want to monitor, and choosing the appropriate enablement option.